AI systems process data at incredible speeds, creating risks for security and compliance. DreamFactory is a secure, self-hosted enterprise data access platform that provides governed API access to any data source, connecting enterprise applications and on-prem LLMs with role-based access and identity passthrough.
Here’s the problem:
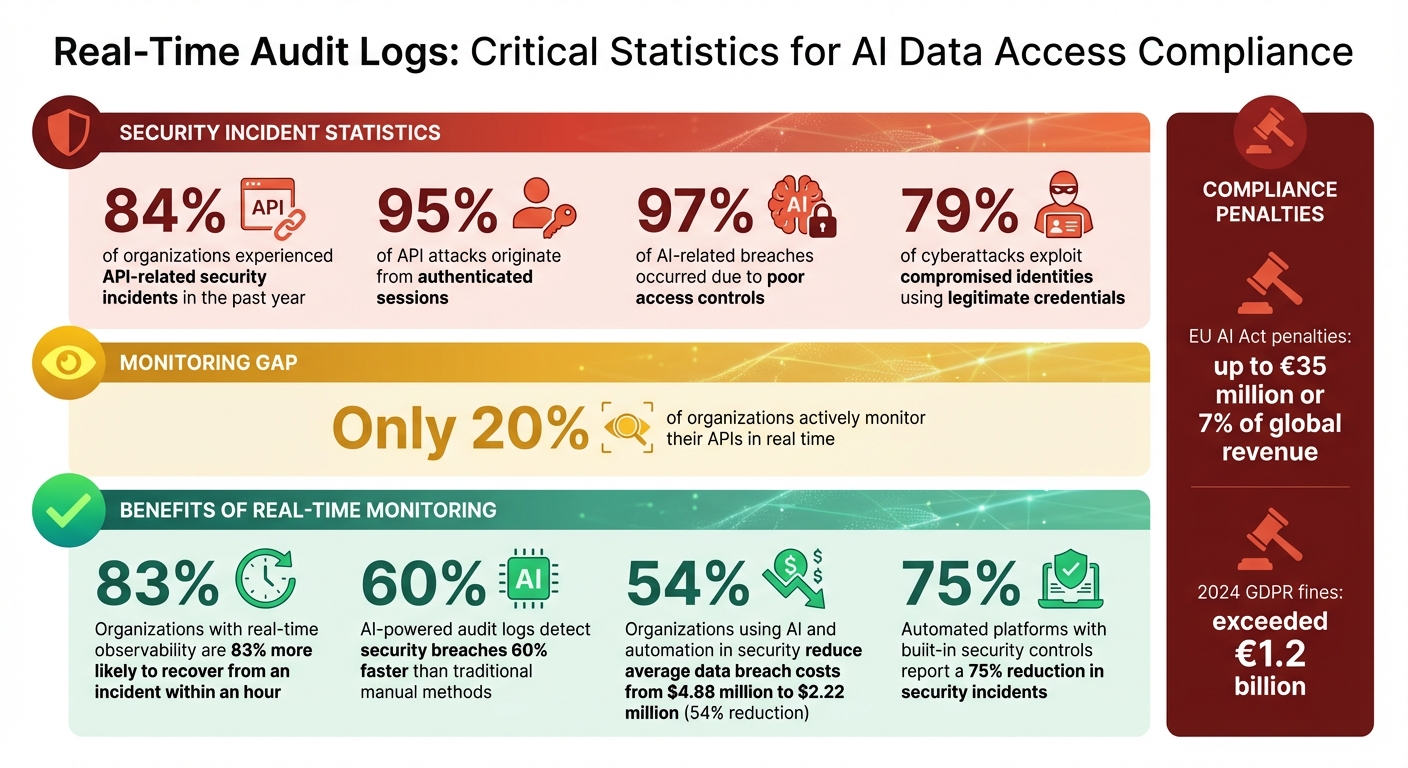
- 84% of organizations faced API-related security incidents in the past year.
- 95% of API attacks come from authenticated sessions.
- 97% of AI-related breaches occurred due to poor access controls.
Real-time audit logs solve this by:
- Creating an unchangeable record of every AI data interaction.
- Tracking who accessed data, what was accessed, and when it happened.
- Supporting compliance with regulations like GDPR, HIPAA, and the EU AI Act.
Without real-time monitoring, organizations risk delayed threat detection, compliance violations, and costly breaches. This article explains how real-time audit logs improve security, ensure compliance, and provide visibility into AI-driven data access.
Real-Time Audit Logs: Key Statistics on AI Security and Compliance
Compliance Challenges in AI Data Access
Scale and Complexity of AI Data Access
AI systems handle data on a scale and speed that far exceeds human capabilities, and that introduces serious compliance challenges. Unlike human analysts who work through datasets gradually, AI pipelines can process enormous volumes in mere seconds, creating a much larger surface area for potential security and compliance risks. This rapid processing also means that AI agents can exploit security gaps or misuse over-permissioned access before traditional monitoring systems even have a chance to react.
A key issue is how AI agents can make chained requests, accessing data across multiple systems almost instantaneously. For instance, an AI agent might pull customer data from one database, financial records from another, and support ticket details - all in milliseconds. This lateral movement of data complicates compliance, especially under frameworks like GDPR, because traditional audit logs often fail to pinpoint which specific data points influenced an AI-generated decision.
Another concern is that AI agents frequently operate using service accounts with broad access credentials. These accounts can inadvertently allow AI systems to query sensitive data far beyond their intended scope. Unlike traditional systems, which rely on fixed, code-based logic, AI operates on dynamic, prompt-driven behavior. This unpredictability can lead to sensitive data being accessed in ways that weren’t anticipated. Legacy API architectures, built with rigid, endpoint-specific logic, simply can’t keep up with the visibility and agility required for AI workloads at scale.
To address these challenges, organizations need advanced audit systems capable of meeting the demands of evolving regulatory standards.
Regulatory Requirements for Continuous Monitoring
Regulatory frameworks like GDPR and HIPAA now mandate that every data query, regardless of how or where it originates, adheres to strict compliance standards. However, traditional logging systems often fall short. They tend to capture only basic details, leaving out critical specifics like which data subjects were accessed or how particular records were used by AI agents.
The stakes for non-compliance are steep. For example, the EU AI Act requires automatic event recording for high-risk systems, with penalties reaching up to €35 million or 7% of global revenue. In 2024 alone, GDPR fines surpassed €1.2 billion. Article 12 of the EU AI Act explicitly mandates the "automatic recording of events" for high-risk AI systems, with a requirement to retain decision-chain records for seven years.
Auditors are now paying closer attention to how organizations monitor AI usage. Security questionnaires increasingly focus on AI governance, pushing companies to go beyond simple policy statements. Regulators now expect timestamped, documented proof of compliance enforcement. Without real-time audit logs that capture key details - such as identity passthrough, policy enforcement, and data subject attribution - organizations will struggle to demonstrate compliance when faced with regulatory scrutiny.
Using AI to Highlight Risky Events in Audit Logs
Why Real-Time Audit Logs Matter
Real-time audit logs turn logging into a proactive security tool rather than just a way to look back at past events. Traditional batch logging systems often process events hours - or even days - after they happen. This delay creates a window of opportunity for threats to go undetected, potentially causing significant harm. With AI systems operating at lightning-fast speeds, these delays are simply not acceptable. Real-time logs capture every interaction as it happens, allowing security teams to detect unusual activity and act quickly to prevent data loss before the situation worsens.
Here’s a staggering statistic: 84% of organizations experienced API-related security incidents in the past year. Yet, only 20% actively monitor their APIs in real time. This gap in monitoring can be costly. Organizations that adopt real-time observability are 83% more likely to recover from an incident within an hour. When AI agents are involved, generating high-speed queries, the difference between immediate detection and delayed discovery can determine whether you block a threat in time or face a full-scale data breach.
Faster Threat Detection and Response
Real-time logs empower SIEM systems to flag suspicious activity as it unfolds. For instance, if an AI service account experiences multiple failed logins from different IP addresses followed by a successful login from an unusual location, real-time monitoring can instantly identify this as a potential credential compromise.
AI data access introduces its own set of monitoring challenges. AI agents might repeatedly retry requests, ask for excessive amounts of data, or display unusual query patterns - any of which could indicate a breach. Real-time monitoring works across three key stages: the request stage (e.g., blocking SQL injection attempts), the response stage (e.g., redacting sensitive information before it leaves the system), and the exfiltration stage (e.g., enforcing limits on row counts and data volumes). This multi-layered approach catches threats that single-point controls might miss.
One of the biggest risks comes from authenticated threats. In fact, 95% of API attacks originate from authenticated sessions. Real-time audit logs help address this by tracking how authenticated users and AI agents interact with systems. For example, if credentials from a former employee are used or an AI agent suddenly requests far more data than usual, real-time logs can trigger immediate action, like invalidating tokens on the spot. Batch-processed logs simply can’t match this level of responsiveness.
| Feature | Traditional Batch Logging | Real-Time Audit Logging |
|---|---|---|
| Detection Speed | Hours or days (post-incident) | Seconds or minutes (during incident) |
| Remediation | Manual, after the fact | Automated (e.g., instant token revocation) |
| Compliance | Periodic audit preparation | Continuous "audit-ready" state |
| AI Suitability | Limited; misses fast AI activity | High; tracks AI-specific patterns |
While speed is critical, real-time audit logs offer another key advantage: they provide solid evidence for compliance.
Regulatory Defensibility and Compliance Proof
Real-time logs don’t just improve security - they also make it easier to meet regulatory requirements. When auditors ask how your organization enforces data access policies, batch logs can only show what happened in the past. Real-time logs, on the other hand, demonstrate that controls like RBAC (Role-Based Access Control), rate limits, and data masking were applied as events occurred. This is especially important for meeting the demands of strict frameworks, such as the EU AI Act’s seven-year record-keeping requirements or SEBI’s five-year audit trails for financial services.
By shifting from static compliance records to dynamic, real-time enforcement, audit logs become more than just paperwork. They demonstrate that your platform is designed for secure, governed operations - something that resonates with auditors and procurement teams alike.
There’s also an added psychological benefit. The "Hawthorne Effect" suggests that people are more likely to follow policies when they know their actions are being logged in real time. This creates an extra layer of accountability, ensuring users stick to established rules while enabling organizations to verify compliance instantly. As a result, real-time audit logs help companies move from reacting to incidents to maintaining a constant state of readiness.
Critical Data Points to Capture in Real-Time Audit Logs
For real-time audit logs to be effective, they must capture both the identity of users and the details of transactions. This combination supports rapid threat detection and ensures compliance with regulatory standards. Missing any essential data point can weaken the ability to reconstruct events and may lead to compliance issues.
Identity Passthrough and User Attribution
Using generic accounts like "svc_account" makes it nearly impossible to trace specific user actions. This lack of accountability not only complicates forensic investigations but also fails to meet regulatory standards that require user-level traceability.
Identity passthrough solves this issue by capturing real user identities - such as "john.smith@company.com" - via integrations like OAuth, SSO, or LDAP. This method ensures that the authenticated user's identity is carried from the application interface, through the API, all the way to the data source. As a result, every action is tied to a specific individual.
"The query doesn't just run. It runs as Alice" - Nic Davidson, Solutions Engineer at DreamFactory
The benefits are clear. 95% of API attacks originate from authenticated sessions, and 79% of cyberattacks exploit compromised identities using legitimate credentials. Identity passthrough ensures that audit logs capture which user's permissions were exploited, limiting the damage and enabling faster incident response.
| Aspect | Identity Passthrough | Service Accounts |
|---|---|---|
| Audit Trail | Logs specific user identities for all actions | Logs generic account entries; lacks traceability |
| Access Control | Enforces user-specific permissions and row-level security | Broad permissions; requires manual filtering |
| Compliance | Meets requirements like SOX, HIPAA, and PCI-DSS | May fail audits due to lack of user-level traceability |
| Security | Limits damage to specific user's permissions | A compromise exposes all accessible data |
While linking actions to real users is critical, capturing additional details is equally important to create a complete audit trail.
Required Access Details
Beyond user identity, audit logs should include additional fields to support thorough incident reconstruction. Key details to capture include:
- User ID: Identifies who performed each action.
- Timestamp: Recorded in UTC to avoid timezone-related errors, with local time (e.g., Eastern, Pacific) displayed in reports.
- Action Description: Specifies the type of action, such as GET, POST, PUT, DELETE, or PATCH.
- Resource Access: Tracks which data or resources were accessed.
- Location Data: Includes IP addresses and geographic information to flag anomalies like after-hours access or unusual locations.
- Result Status: Indicates whether actions were successful or failed.
For AI systems, it's also essential to log query parameters generated by the large language model (LLM) and ensure results align with the user's permissions.
This detailed metadata provides an immutable record that supports compliance with frameworks like GDPR, CCPA, and HIPAA.
DreamFactory simplifies this process by automatically capturing these critical data points through governed REST API endpoints. By integrating with OAuth, LDAP, or SSO, the platform ensures every AI query is tied to the real user who initiated it - not a generic service account - while maintaining a detailed log of what data was accessed, when, and from where.
How to Implement Real-Time Audit Logging
Setting up real-time audit logging isn't just about turning on database logs. To meet strict regulatory demands and handle the intricate data access patterns of AI systems, you need a multi-layered approach. This approach should capture every interaction, from the initial prompt to the final data query, while ensuring logs are tamper-proof and actionable. The ultimate goal? An unchangeable record that supports quick threat detection and regulatory compliance.
Centralized Log Management and Retention
Storing logs locally can create blind spots and make it harder to analyze data across systems. Instead, organizations should adopt centralized platforms like ELK Stack (Elasticsearch, Logstash, Kibana), Splunk, or cloud-native solutions like AWS CloudWatch for better visibility across AI services.
To protect logs from tampering, implement Write-Once-Read-Many (WORM) storage or append-only files. Even if attackers gain admin access, they won't be able to modify or delete logs. Use cryptographic hashing (e.g., SHA-256) and digital signatures to detect any unauthorized changes.
For retention, a tiered storage approach works best:
- Hot storage: For recent logs needed for immediate monitoring and response.
- Warm storage: For logs up to a year old, useful for audits and analysis.
- Cold storage: For long-term retention, meeting compliance standards like SOX or HIPAA.
Index Lifecycle Management (ILM) policies can automate the movement of logs between these tiers based on age and compliance needs.
| Storage Tier | Retention Period | Use Case | Access Speed |
|---|---|---|---|
| Hot | 0-30 days | Real-time monitoring and incident response | Immediate |
| Warm | 1-12 months | Forensic analysis and compliance audits | Minutes |
| Cold | 1-7 years | Long-term regulatory compliance | Hours |
This framework also makes it easier to integrate with Security Information and Event Management (SIEM) platforms for real-time threat detection.
Integration with SIEM and Incident Response Systems
Centralized logs become even more powerful when paired with a SIEM platform. Tools like Logstash can forward data using protocols like UDP or syslog, enabling SIEMs to perform correlation analysis. For instance, they can link multiple failed logins with subsequent successful access attempts from unusual locations.
AI-powered audit logs can detect security breaches 60% faster than traditional manual methods. Additionally, organizations that use AI and automation in their security processes report a significant drop in the average cost of data breaches - from $4.88 million to $2.22 million, a 54% reduction.
To make the most of these systems, set up multi-tiered alerts based on severity. For example:
- Low-priority anomalies (like unusual login times) can trigger email notifications.
- High-severity events (e.g., 100 failed login attempts within an hour) should activate immediate incident response protocols.
In high-traffic AI environments, tools like Redis can help with distributed rate limiting and log caching, ensuring performance doesn't take a hit across server clusters.
"AI doesn't just flag an issue - it understands the context, helping you pinpoint the root cause before small issues escalate into major disruptions." - LogicMonitor
API Abstraction for Governed Data Access
A secure API gateway between AI systems and databases is one of the most effective ways to enforce controlled data access. This abstraction layer supports zero-trust principles, role-based access control (RBAC), and identity passthrough, all while generating detailed audit logs automatically.
DreamFactory provides a governed gateway, ensuring AI systems access data through REST APIs instead of direct database connections. The platform logs critical details - user identity (via OAuth, LDAP, or SSO), timestamps, action types, accessed resources, and result statuses - without requiring custom code. It enforces role-based access control at multiple levels, adhering to the principle of least privilege.
Since standard API timeouts of 30 seconds are often too short for complex AI tasks like large language model (LLM) inference, configure timeouts to at least 300 seconds (5 minutes). For sensitive data, consider hashing API-specific elements like prompts and responses. This ensures reproducibility while avoiding the storage of sensitive plain text.
Organizations that adopt automated platforms with built-in security controls report a 75% reduction in security incidents. Deploying these platforms in on-premises, air-gapped, or private cloud environments ensures data remains within your infrastructure while maintaining complete audit visibility. This approach directly addresses the compliance and security challenges discussed earlier, creating a system that's always audit-ready.
Conclusion
This article shed light on how real-time audit logs can transform AI data access challenges into opportunities for compliance and security. By recording every interaction - covering user identity, timestamps, accessed resources, and outcomes - organizations create the reliable evidence required by regulations like GDPR, HIPAA, SOC 2, and FedRAMP. The move from reactive investigations to proactive monitoring allows threats to be identified up to 60% faster than with traditional methods, while automated reporting eliminates the need for manual audit preparation.
To ensure this level of security, implementing a secure API gateway is critical. It enforces zero-trust principles, role-based access control (RBAC), and generates tamper-proof audit logs.
"Don't let LLMs write SQL. Put a secure API gateway between AI and your databases. Enforce zero-trust, parameterization, RBAC, masking, and full-fidelity audit logs." - Kevin McGahey, Solutions Engineer and Product Lead, DreamFactory
DreamFactory is a secure, self-hosted enterprise data access platform that provides governed API access to any data source, connecting enterprise applications and on-prem LLMs with role-based access and identity passthrough. Every request is tied to an authenticated user's identity, not a generic service account, which preserves row-level security and creates detailed audit trails. The platform integrates seamlessly with existing OAuth, LDAP, or SSO systems, and routes audit data directly into SIEM tools like Splunk or ELK Stack.
DreamFactory deploys on-premises, in air-gapped, private cloud, edge, or hybrid environments, ensuring data remains within your infrastructure. This is a vital feature for the 53.8% of regulated organizations that prioritize data sovereignty for AI workloads. With over 30 connectors to databases, file storage, and services, you gain full visibility and control - an essential safeguard, especially when 97% of AI-related breaches occurred in organizations lacking proper access controls.
Real-time audit logs are no longer optional; they are a cornerstone for meeting compliance requirements, preventing security breaches, and maintaining trust in AI-powered systems. By adopting real-time audit logs, organizations can confidently navigate regulatory landscapes while building a secure and transparent future for AI data access.
FAQs
What makes an audit log “real-time” for AI data access?
An audit log is described as "real-time" for AI data access when it enables instant detection of security risks and delivers immediate insights. This is made possible through automated tracking systems and dashboards that actively monitor and report data usage. These tools ensure that compliance and security measures are upheld without any delays.
What fields should we log to prove AI access compliance?
To maintain compliance with AI access standards, it's important to log critical details. These include user access records, prompt inputs, AI outputs, system modifications, decision-making processes, timestamps, model versions, and context. Keeping these logs ensures transparency, accountability, and helps meet regulatory requirements.
How do we make audit logs tamper-proof and retention-ready?
To keep audit logs secure and ready for retention, consider using hash chains, structured events, and off-machine replication. Save events in append-only JSONL files and send them to a remote dashboard for independent verification. This method not only protects the integrity of your logs but also ensures they are accessible for compliance purposes.
Kevin Hood is an accomplished solutions engineer specializing in data analytics and AI, enterprise data governance, data integration, and API-led initiatives.
























 Blog
Blog
