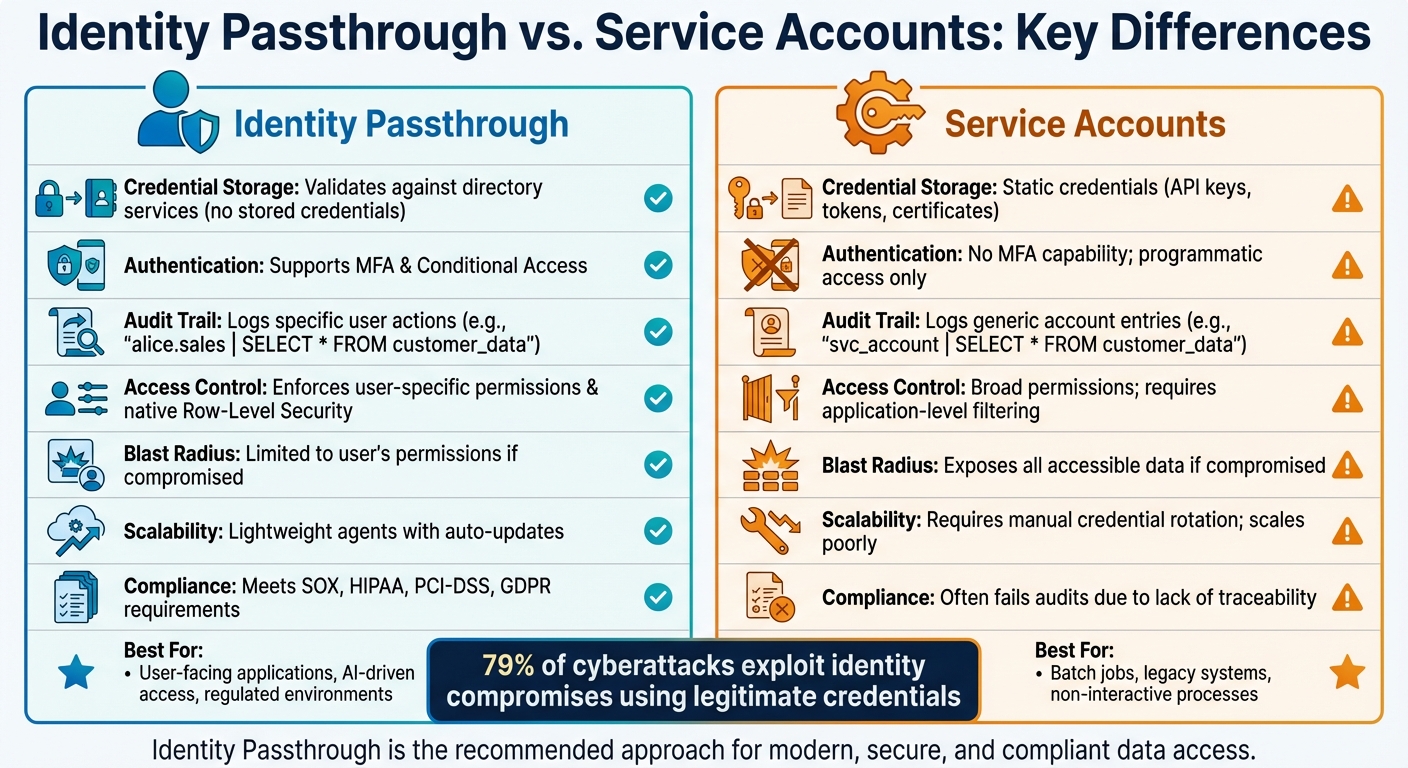
When it comes to secure enterprise data access, two approaches dominate: Identity Passthrough and Service Accounts. Here's the core difference:
- Identity Passthrough: Ensures a user's identity is preserved throughout the entire data request process. This method ties actions to individual users, enforces role-based permissions, and creates detailed audit logs. It’s ideal for regulated industries and user-facing applications.
- Service Accounts: Uses shared, static credentials to allow applications or automated processes to access data. While simpler, it lacks user-level traceability and poses greater security risks if compromised.
Quick Overview:
- Identity Passthrough is better for user-specific security, compliance, and detailed audit trails.
- Service Accounts are better for non-interactive processes like batch jobs or legacy systems.
Quick Comparison:
|
Aspect |
Identity Passthrough |
Service Accounts |
|---|---|---|
|
Credential Storage |
Validates against directory services |
Static credentials (e.g., API keys) |
|
Authentication |
Supports MFA, Conditional Access |
No MFA, programmatic access only |
|
Audit Trail |
Logs specific user actions |
Logs generic account activity |
|
Access Control |
Enforces user-specific permissions |
Broad permissions, app-level filtering |
|
Use Cases |
Regulated environments, AI-driven access |
Batch jobs, legacy systems |
Both methods have their place, but identity passthrough is the go-to for modern, secure, and compliant data access.
Identity Passthrough vs Service Accounts: Security and Compliance Comparison
Pass-Through Authentication Explained (With Packet Capture & Setup Demo)
What Is Identity Passthrough?
Identity passthrough is an authentication approach that ensures a user's identity is maintained throughout every step of a data request - from the application interface to the database. Instead of relying on shared service accounts or generic credentials, it uses existing identity systems like OAuth, LDAP, or SSO to verify who is accessing the data. This method ensures the user's identity remains intact across all layers. For instance, if Alice logs into an app using her company credentials via Active Directory or Okta, the database recognizes her as "Alice." This makes sure that all access controls, permissions, and security policies tied to her account are automatically enforced.
One major advantage is that this method removes the need to store passwords in the cloud. Microsoft’s Entra pass-through authentication is a great example - it validates credentials in real time against on-premises directories like Active Directory, using an outbound-only agent that relies on certificate-based authentication, which renews automatically every few months.
How Identity Passthrough Works
When a user logs in using OAuth, SAML, or LDAP, the system captures an identity token that contains credentials and group memberships. This token is then forwarded by an agent for real-time validation using certificate-based methods that renew automatically. Once validated, the user’s identity is passed down to the database, where specific access controls - like row-level or field-level security - are applied based on their permissions.
For example, in a DreamFactory setup with Oracle, if Alice initiates a query, her username is logged, and the query runs under her identity. As Nic Davidson from DreamFactory explains:
"The query doesn't just run. It runs as Alice."
This setup also integrates with advanced security measures, such as Multi-Factor Authentication (MFA), blocking legacy protocols, and defending against brute force attacks. The result? Every request is explicitly validated while maintaining a seamless user experience.
Benefits of Identity Passthrough
The security benefits are substantial. By keeping the user’s identity intact, identity passthrough enables precise access controls like row-level security and creates detailed audit trails tied directly to individual users. This is especially important given that 79% of cyberattacks now exploit identity compromises using legitimate credentials. If a session is compromised, the damage is limited to that user’s specific permissions.
It also reduces operational complexity. There's no need to manage separate service accounts for different applications or AI systems. Automatic updates and bug fixes for the agent eliminate the hassle of manual intervention, such as password syncing or configuring complex networks. This also removes the need for a separate governance framework.
Audit logs become far more actionable and transparent. Instead of generic entries like "service_account | SELECT * FROM financial_records", logs now show detailed actions, such as "alice.sales | SELECT * FROM customer_data." This level of visibility is essential for meeting compliance standards in the US, such as GDPR, HIPAA, SOX, and PCI-DSS, as it directly ties data access to specific users.
For AI-driven data access, identity passthrough ensures that AI systems operate within the boundaries of the authenticated user’s permissions. This prevents the use of high-privilege accounts while maintaining strong security and clear, user-specific audit logs.
What Are Service Accounts?
Service accounts are a type of non-human identity designed to allow applications or automated processes to access data without relying on individual user credentials. Unlike identity passthrough, which keeps the user's identity intact during data access, service accounts operate using generic credentials. These accounts essentially represent the application itself rather than any specific user.
As described in Google Cloud documentation:
"A service account is a special kind of account typically used by an application or compute workload... rather than a person."
Think of service accounts as a bridge between your application and the data it needs. For example, when an app queries a SQL Server database or retrieves files from a storage bucket, it uses the service account's credentials to authenticate. The database only recognizes the service account, not the identity of the user who initiated the request. This differs significantly from identity passthrough, where the actual user's identity is passed along to the data layer.
How Service Accounts Work
To use a service account, you first create it and assign static credentials, such as an API key, JSON file, or username/password. These credentials are then embedded within your application's configuration or environment variables. Once configured, the application can authenticate automatically whenever it needs to access data.
Service accounts are assigned roles through IAM (Identity and Access Management), which define what resources they can access. For instance, you might create a service account called svc_analytics with read-only permissions for your customer database. Regardless of which employee views the analytics dashboard, all queries would run using the svc_analytics credentials. It's worth noting that some cloud platforms limit the number of service accounts you can create per project - for example, to 100 accounts.
Common scenarios for service accounts include:
- CI/CD pipelines
- Kubernetes Pods accessing secrets
- AI agents querying enterprise data
In Kubernetes, each namespace is automatically assigned a default service account when created. However, this account starts with minimal permissions. To improve security, modern implementations often use short-lived, automatically rotating tokens. For example, Kubernetes introduced the TokenRequest API in version 1.22, reducing the risks tied to static credentials.
Next, let's explore the operational and security challenges that come with using service accounts.
Challenges of Service Accounts
One major downside of service accounts is limited visibility. Since all activity is logged under a shared identity, it's impossible to trace specific actions back to individual users. This lack of transparency can create compliance headaches for industries bound by regulations like HIPAA, SOX, or PCI-DSS. For example, instead of seeing "alice.sales | SELECT * FROM customer_data", logs will only show "svc_account | SELECT * FROM customer_data."
Another issue is that service accounts often have broad permissions. If a service account is compromised, all the data it can access becomes vulnerable. Static credentials stored in configuration files are particularly attractive targets for malware and attackers. Managing these accounts adds to administrative complexity, especially when dealing with tasks like key rotation, identifying unused accounts (inactive for 90+ days), and disabling dormant accounts (no authentication for 180+ days). While security tools can help flag these issues, the process remains labor-intensive.
Service accounts also bypass user-level security controls. They don't enforce row-level security based on the actual user making the request, which means they can return data that the end-user shouldn't access. If a user session is exploited, the damage is limited to that user's permissions. However, if a service account is compromised, everything it can access is at risk. This is particularly concerning in AI-driven systems, where vulnerabilities like prompt injection attacks have a 91% success rate against unprotected LLM agents.
Key Differences Between Identity Passthrough and Service Accounts
When comparing identity passthrough and service accounts, the distinctions in security, scalability, and governance are important for enterprise-level data access.
The main difference lies in credential management. Identity passthrough validates credentials directly against on-premises Active Directory or similar authentication sources. In contrast, service accounts depend on static credentials like API keys, tokens, certificates, or SSH keys. This means identity passthrough avoids storing credentials entirely, reducing risks, while service accounts create a persistent attack surface by retaining these credentials.
From a security standpoint, identity passthrough offers more robust protections. It supports Multi-Factor Authentication (MFA) and Conditional Access policies by leveraging existing authentication setups. Service accounts, however, can't use MFA due to their non-human nature, and their activity often goes unnoticed in standard audit logs. According to NIST SP 800-63-4, service accounts operate outside typical identity governance frameworks, leaving gaps in visibility that identity passthrough avoids. With 79% of cyberattacks involving identity compromise, service accounts - with their elevated privileges and constant operation - are prime targets.
Scalability is another critical area where the two approaches differ. Identity passthrough uses lightweight agents that require minimal setup, automatically renew certificates, and make only outbound connections - eliminating the need for perimeter network installations. On the other hand, service accounts require manual credential management for each application or workload, creating significant administrative overhead as infrastructure grows. For organizations managing hundreds or thousands of applications, this difference can dramatically affect operational efficiency.
These distinctions also influence governance and compliance. Identity passthrough integrates seamlessly with user authentication frameworks like OAuth, LDAP, and SSO, ensuring better alignment with regulations like SOX, HIPAA, and PCI-DSS. Service accounts, however, often fail audits due to their lack of user-level traceability.
Comparison Table
|
Aspect |
Identity Passthrough |
Service Accounts |
|---|---|---|
|
Credential Storage |
Validates against existing directory services |
Static credentials (API keys, tokens, certificates) stored in configuration |
|
Authentication |
Supports MFA and Conditional Access policies |
No MFA capability; programmatic access only |
|
Audit Trail |
Logs specific user identities for all actions |
Logs generic account entries |
|
Governance |
Integrates with OAuth, LDAP, SSO |
Operates outside human identity governance |
|
Access Control |
Enforces user-specific permissions and native Row-Level Security |
Broad permissions; requires application-level filtering |
|
Blast Radius |
Limited to specific user's permissions if compromised |
Exposes all accessible data if compromised |
|
Scalability |
Uses lightweight agents with auto-updates |
Requires manual credential rotation; scales poorly |
|
Compliance |
Meets SOX, HIPAA, PCI-DSS requirements |
Often fails audits due to lack of traceability |
The differences outlined above show why identity passthrough is often preferred for secure, scalable, and governed data access in enterprise environments.
Use Cases for Identity Passthrough
Identity passthrough brings together security, audit trails, and authentication in a seamless way. It ensures compliance with stringent regulations like GDPR, HIPAA, SOX, and PCI-DSS by logging actions under the actual user's identity. Additionally, it carries user attributes directly to the database, enabling segmented access to data across federated organizations.
One of its standout capabilities is row-level filtering, which eliminates the need for complex application-level permission logic. For instance, a sales representative querying revenue data would only see information related to their assigned accounts. With these compliance and segmentation advantages, let’s dive into how AI-driven data access benefits from identity passthrough.
AI-Driven Data Access with DreamFactory
AI systems come with their own set of security challenges, particularly when it comes to accessing data they shouldn't. DreamFactory steps in as a protective layer, ensuring all AI queries respect the authenticated user's permissions.
"Identity passthrough means the AI system doesn't become the identity. It acts on behalf of the authenticated user - so permissions, row-level security, and audit logs still apply." - Nic Davidson, January 27, 2026
DreamFactory integrates with existing authentication methods like OAuth, LDAP, or SSO, removing the need for AI to directly connect to databases or understand their schemas. This approach not only enhances security but also provides built-in threat protection and audit logging. Whether your deployment is on-premises, in private or hybrid clouds, or at the edge, your data stays within your infrastructure, and every query is tied back to the individual user.
Governance in Regulated Environments
In regulated industries, having precise control and traceability over data access is non-negotiable. For example, when HR managers use AI tools for employee reviews, identity passthrough ensures they can only access the data they're authorized to see, with all actions logged under their identity.
"GDPR data access logs, SOX change-tracking requirements, and HIPAA audit trails all require that records show which person accessed which data - not merely which application." - DreamFactory Docs
This approach also reduces security risks by limiting exposure to a single user's permissions. Instead of relying solely on application-level logic, authorization is enforced at the database or gateway level. If a session is compromised, the damage is contained to that specific user's permissions, keeping the rest of the database secure. For organizations still using legacy systems like SQL Server, Oracle, or ERPs, identity passthrough offers a way to securely integrate these systems with modern AI and web applications while maintaining their existing security protocols.
When to Use Service Accounts
Service accounts are essential for automated, non-interactive processes where identity passthrough isn’t feasible. These accounts shine in scenarios where no human user is present to provide an identity token - like nightly batch jobs, system-to-system integrations, or scheduled data pipelines. They’re a practical solution when modern identity protocols aren’t in play.
They’re particularly handy for legacy systems that don’t support modern protocols like OAuth or SAML. Many older databases and ERP systems lack row-level security, making shared service accounts the go-to option for connecting. In such setups, the application layer has to handle permissions and data filtering manually.
Beyond legacy systems, service accounts are helpful in testing and development environments. They allow for faster setup and testing without the complexity of configuring full identity passthrough. Similarly, they’re great for anonymous or public data access scenarios, where identifying individual users isn’t necessary. In these cases, a simple API key tied to a service account often does the job.
That said, using service accounts responsibly is critical. Always follow the principle of least privilege - grant only the permissions needed for the task. Rotate credentials monthly, store them securely in tools like HashiCorp Vault or AWS Secrets Manager instead of .env files, and monitor for unusual activity, such as unexpected access locations or high request volumes.
However, there are trade-offs to consider. For instance, audit logs will reflect generic entries like "service_account" instead of specific usernames, which can reduce visibility in non-interactive systems. If credentials are compromised, the damage could extend to the entire database rather than being limited to a single user session. While identity passthrough is ideal for detailed user-level security, service accounts remain a key tool for legacy and automated workflows.
Conclusion
Identity passthrough is reshaping enterprise data access security by using real-time validation of user credentials and leveraging existing authentication systems. This approach eliminates the risks tied to stored secrets, addressing a critical vulnerability since 79% of cyberattacks exploit identity compromises through legitimate credentials. For modern organizations, this marks a significant step forward in securing sensitive data.
While service accounts still have their place - such as in legacy systems, batch jobs, or non-interactive processes - identity passthrough is the better option for user-facing applications, AI-driven data access, and regulated environments. It delivers benefits like granular security controls, detailed audit logs, and reduced risk exposure that service accounts cannot match.
For those ready to adopt identity passthrough, DreamFactory offers a seamless solution. Acting as an abstraction layer, it integrates with OAuth, LDAP, or SSO systems to provide governed access, complete with audit logging and threat protection. Whether your infrastructure is on-premises, air-gapped, private cloud, or hybrid, DreamFactory enables secure data access without the need for direct database connections.
To make the transition, focus on high-risk workloads first. Start with user-facing applications where the security and compliance benefits are most urgent. In cloud environments, tools like AWS IAM Roles Anywhere or Azure Workload Identity Federation can help eliminate static credentials. For hybrid setups, lightweight agents can validate credentials against on-premises Active Directory without storing passwords in the cloud.
As enterprises increasingly rely on AI and embrace zero trust architectures, identity passthrough is no longer optional - it’s essential. The challenge now is to implement it swiftly while ensuring smooth operations.
FAQs
Can we use both identity passthrough and service accounts together?
Yes, you can use both methods together in DreamFactory. Identity passthrough links external user identities (like SSO) to specific roles, enabling detailed user-level audit logging and governance. On the other hand, service accounts offer programmatic access that isn’t tied to individual users, using API keys or tokens. By combining these approaches, enterprises can maintain strict governance and auditability while also supporting automation and seamless application-level integrations.
What changes are needed in our apps and databases to enable identity passthrough?
To set up identity passthrough, update your applications to work with external identity providers (IdPs) like Okta, ADFS, or Azure AD. Use protocols such as SAML, OAuth, or OpenID Connect to manage authentication. Make sure authenticated user identities are transmitted through tokens or assertions.
Additionally, configure your database to log specific user identities instead of relying on generic service accounts. While schema changes are usually unnecessary, your audit logging system must be capable of tracking and recording user identities effectively.
How can static service account secrets be replaced without disrupting automation?
Switch out static service account secrets for identity passthrough methods that integrate with your current authentication systems (like OAuth, LDAP, or SSO). This approach enables automation to authenticate dynamically with managed tokens or credentials, minimizing the security risks associated with static secrets. Tools such as DreamFactory offer support for identity passthrough, providing secure and controlled access to enterprise data without disrupting automation processes.
Konnor Kurilla is a technical engineer with experience supporting API-driven workflows, troubleshooting backend systems, and developing documentation that empowers users to understand and utilize their technology. Blending customer-focused thinking with hands-on technical skills, he helps bridge the gap between product complexity and user clarity.
























 Blog
Blog


