Hybrid AI systems need secure ways to manage user identities across cloud and on-premises environments. Identity passthrough ensures that AI systems operate under the permissions of the actual user, not a shared service account. This approach reduces risks tied to credential theft, improves auditability, and supports compliance with regulations like GDPR and HIPAA.
Key methods for identity passthrough include:
- Password Hash Synchronization (PHS): Syncs hashed passwords to the cloud, enabling authentication without constant on-premises connectivity.
- Pass-Through Authentication (PTA): Validates credentials in real-time against on-premises systems, ensuring passwords are never stored in the cloud.
- DreamFactory Identity Passthrough: Maintains user identity throughout the request process, enforcing granular permissions at the database level.
Quick Takeaway:
For organizations prioritizing simplicity, PHS is a good starting point. PTA is ideal for avoiding cloud password storage. However, for detailed user-level controls and compliance in hybrid AI setups, DreamFactory provides the most secure and precise solution.
SC-300: Implement Hybrid Identity in Microsoft Entra
1. Password Hash Synchronization (PHS)
Password Hash Synchronization (PHS) is a method used in hybrid authentication setups, where password hashes from an on-premises Active Directory are synced to Azure AD. Instead of transferring plaintext passwords, the system generates hashes using algorithms like SHA-256 or PBKDF2 on-premises and then syncs these to the cloud. This approach allows cloud-based systems to perform API authentication to validate credentials without needing constant connectivity to on-premises servers. Let’s break down how PHS supports hybrid AI deployments through its encryption and compliance features.
Security and Compliance
PHS ensures that plaintext passwords never leave the on-premises environment, significantly reducing the risk of exposure. By using one-way hashing, it protects against replay attacks and credential theft, cutting breach risks by as much as 99%. The synchronization process is further secured with encrypted channels via TLS 1.2 or higher, aligning with compliance frameworks like GDPR and HIPAA. For hybrid AI deployments, this means AI systems can securely access sensitive data while adhering to strict security standards. However, storing password hashes in the cloud does introduce a potential attack surface compared to real-time validation methods.
Integration with Existing Infrastructure
PHS works seamlessly with Active Directory and LDAP systems using tools like Azure AD Connect. It also supports OAuth and Single Sign-On (SSO) passthrough, requiring minimal changes to existing configurations. However, the synchronization process isn’t instantaneous - it can take up to 30 minutes. According to a 2023 Gartner report, 65% of enterprises implementing hybrid identity solutions favor PHS for its balance of security and ease of management.
Deployment Flexibility
One of the strengths of PHS is its adaptability across different deployment models. It supports on-premises, cloud, hybrid, and edge setups without requiring custom authentication agents for every AI node. The system can sync up to 500,000 objects within a 30-minute window, making it scalable for large enterprises. This scalability is especially important for AI workloads spread across Kubernetes clusters or multi-cloud environments, where PHS ensures secure synchronization without constant reliance on on-premises systems.
Auditability and Observability
PHS provides robust logging capabilities through Azure AD sign-in reports and diagnostics, capturing synchronization outcomes, user sign-ins, and anomalies like impossible travel alerts. These logs integrate with SIEM tools like Splunk, offering real-time monitoring and a complete audit trail. This level of traceability supports secure identity management. However, when PHS is used with shared service accounts instead of individual identities, audit logs may only reflect generic account activity. This can complicate compliance with regulations like SOX and HIPAA, which often require detailed user-level accountability.
2. Pass-Through Authentication (PTA)
Pass-Through Authentication (PTA) verifies user credentials in real-time by connecting directly to existing identity providers like Active Directory, LDAP, OAuth, or SSO. Instead of storing passwords, it routes authentication requests to your directory, ensuring your on-premises infrastructure remains the authoritative source for user identities and permissions.
Security and Compliance
With PTA, credentials are never stored in multiple locations, which minimizes potential vulnerabilities. When an AI system accesses data, it does so on behalf of a specific authenticated user rather than using a shared service account with excessive permissions. This approach limits the potential impact of a compromised session to the permissions tied to that user’s account. This containment strategy is crucial for reducing identity-based risks.
PTA also supports Multi-Factor Authentication (MFA) and Conditional Access policies, creating detailed audit trails that link every data access action to a specific user. These features are essential for adhering to regulations like GDPR, HIPAA, SOX, and PCI-DSS. By aligning with these compliance standards, PTA ensures secure integration with your existing authentication systems.
Integration with Existing Infrastructure
PTA integrates smoothly with your current authentication setup without requiring extensive changes. It uses credentials or tokens from established providers and forwards validation requests to your directory. This means users don’t need separate credentials for AI systems, and IT teams avoid the hassle of managing additional password resets or credential rotations.
Organizations using PTA report up to 99.9% uptime for authentication in hybrid setups. Furthermore, Microsoft highlights that PTA can lower password-related breach risks by 50% compared to synchronization-based methods in hybrid environments.
Deployment Flexibility
Since PTA doesn’t rely on synchronizing credentials across different environments, it offers deployment flexibility for AI workloads. You can operate AI systems on-premises, in private or public clouds, or even in air-gapped environments, all while maintaining centralized authentication. For hybrid setups, outbound-only agents using certificate-based authentication simplify network configurations by avoiding inbound firewall adjustments.
PTA also supports deployment on various platforms, including bare-metal VMs (Linux or Windows), private clouds, and containerized environments like Docker or Kubernetes, enabling horizontal scaling. This flexibility ensures secure, governed AI data access across distributed setups. As of 2023, 78% of enterprises utilize hybrid identities, with 62% citing regulatory compliance as the primary reason for adopting hybrid architectures.
Auditability and Observability
PTA provides a comprehensive audit trail, linking each data access action to a specific user. Unlike service accounts, which log generic activity (e.g., "svc_account"), PTA records detailed user-specific activity (e.g., "alice.sales"). This level of traceability ensures full visibility into who accessed what data and when.
For added compliance, PTA agents can be configured on separate servers from domain controllers, with sign-in logs actively monitored. Audit logs also include contextual information, such as the user’s role, department, and permission level at the time of access, enhancing transparency and security.
3. DreamFactory Identity Passthrough
DreamFactory Identity Passthrough builds on PHS and PTA by creating a secure layer between AI systems and enterprise databases. This approach ensures AI systems access data through controlled APIs, maintaining strict identity controls without needing direct database connections. Instead of managing schemas or credentials separately, the platform allows AI to operate within the bounds of authenticated user permissions at every stage.
Security and Compliance
DreamFactory's identity passthrough enhances security in hybrid environments where access control is critical. By carrying the user's identity from the interface to the database, all queries inherit the authenticated user's privileges. This is especially important when considering that 79% of cyberattacks exploit identity compromises using legitimate credentials.
The platform eliminates vulnerabilities tied to shared service accounts. It enforces user-specific row-level security (RLS) and field-level masking directly at the database level. Every action is logged under individual user identities, such as "alice.sales", instead of generic entries like "service_account." This approach supports compliance with regulations like GDPR, HIPAA, SOX, and PCI-DSS.
Integration with Existing Infrastructure
DreamFactory integrates seamlessly with existing authentication systems, including OAuth 2.0, OpenID Connect, JWT, LDAP/AD, and SAML/SSO, without storing or synchronizing additional credentials. It maps identity provider attributes (e.g., group, department, job title) to DreamFactory roles directly.
The platform supports over 30 connectors, including Snowflake, Databricks, Oracle, SQL Server, MongoDB, S3, SAP, and Salesforce. It automatically generates REST APIs with full documentation. For hybrid environments, outbound-only agents or VPN tunnels validate credentials against on-premises directories without storing passwords in the cloud. This integration ensures smooth operations, paving the way for flexible deployment options.
Deployment Flexibility
DreamFactory offers deployment options that suit various environments, including on-premises, air-gapped networks, private clouds, edge devices, or hybrid setups. This ensures sensitive data never leaves your infrastructure. The platform supports Linux, Windows, Docker, Kubernetes (via Helm), ARM64 devices, and IoT gateways, enabling horizontal scaling across diverse architectures. Local RBAC enforcement is synchronized with audit logs, ensuring security across all deployments.
This flexibility aligns with the Sovereign AI movement, where regulatory and data sovereignty concerns restrict cloud-based processing of sensitive information. Organizations can centralize authentication while running AI workloads in isolated or hybrid environments.
Auditability and Observability
DreamFactory ensures complete audit logging, capturing user identity, query parameters, and responses for every data access request. It can pass user identity into the database session context (e.g., using SET SESSION application_name in PostgreSQL), leveraging native database audit logs. This dual-layer logging provides full visibility into AI interactions while maintaining security.
Additional observability features include integration with Prometheus and Grafana, along with rate limiting and caching. For extended AI processes, timeouts can be configured for at least 300 seconds. A built-in Model Context Protocol (MCP) server also allows AI assistants to query databases through governed API endpoints, ensuring controlled and secure interactions.
Advantages and Disadvantages
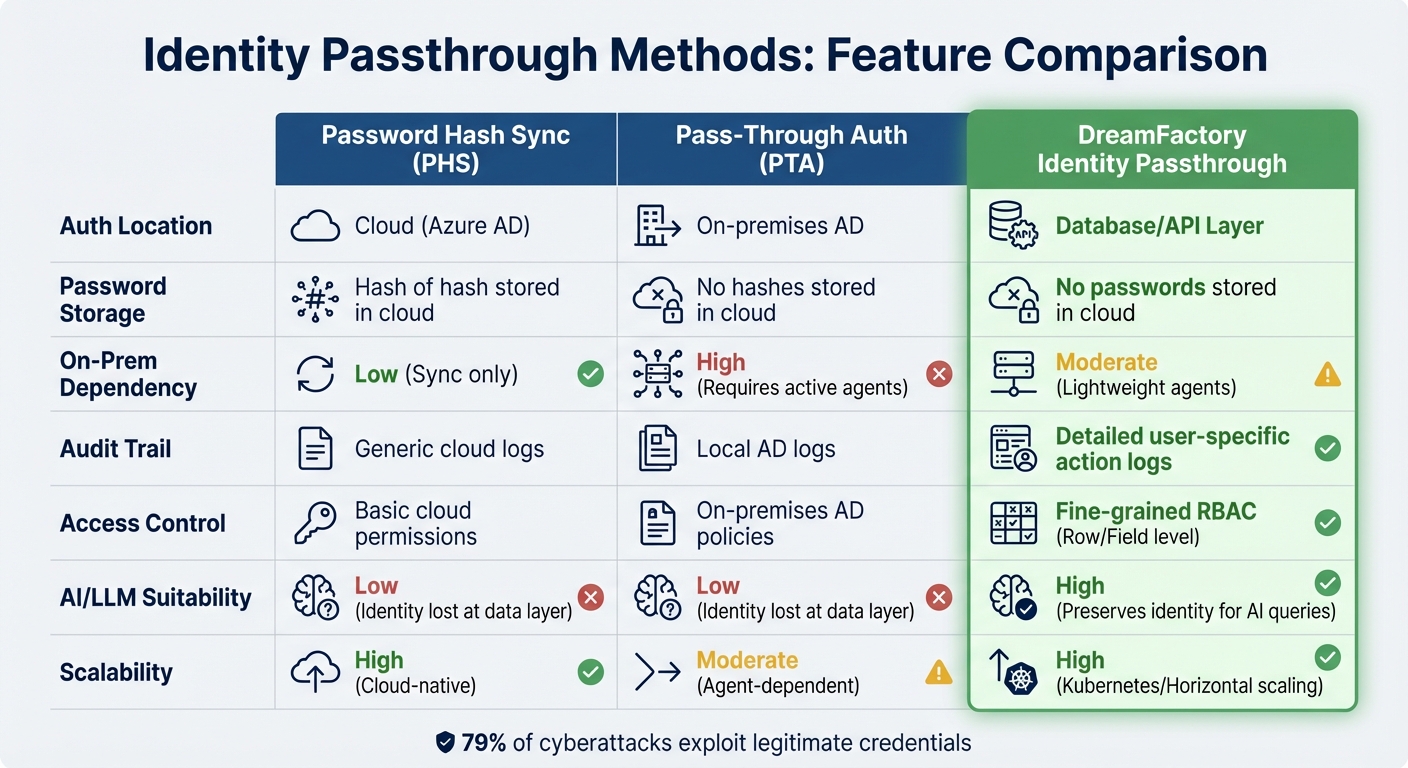
Identity Passthrough Methods Comparison: PHS vs PTA vs DreamFactory
When it comes to securing hybrid AI deployments, each authentication method has its own strengths and weaknesses. Let’s break them down:
Password Hash Synchronization (PHS) is known for its straightforward setup and minimal reliance on on-premises infrastructure, making it a great fit for cloud-native environments. It stores password hashes in the cloud, double-hashed using SHA256, which simplifies authentication but also creates a persistent risk of attack. Additionally, PHS doesn’t maintain individual user context when AI systems interact with data through service accounts, which can limit its effectiveness in scenarios requiring granular control.
Pass-Through Authentication (PTA) eliminates the concern of storing passwords in the cloud by validating credentials against on-premises Active Directory in real time. A single PTA Authentication Agent can handle between 300 and 400 authentications per second on a standard 4-core CPU with 16 GB RAM. For high availability, Microsoft advises deploying at least three agents, with a maximum of 40 agents per tenant. While PTA ensures passwords stay local, it still struggles to maintain user-level context at the database layer, especially when AI systems execute queries.
DreamFactory Identity Passthrough stands out by preserving the authenticated user's identity throughout the entire request process - from the AI interface to the data source. This ensures that queries are executed under specific user permissions rather than generic service accounts. Features like row-level security, field-level masking, and detailed audit logging ensure user entitlements are strictly enforced. DreamFactory also automates REST API generation for over 20 databases, simplifying deployment while maintaining security. However, it requires longer script timeouts (at least 300 seconds) to prevent deadlocks in complex setups. By executing every query under the proper user identity, this approach strengthens security and compliance, especially for hybrid AI deployments.
Here’s a quick comparison of these methods across key aspects:
| Feature | Password Hash Sync (PHS) | Pass-Through Auth (PTA) | DreamFactory Identity Passthrough |
|---|---|---|---|
| Auth Location | Cloud (Azure AD) | On-premises AD | Database/API Layer |
| Password Storage | Hash of hash stored in cloud | No hashes stored in cloud | No passwords stored in cloud |
| On-Prem Dependency | Low (Sync only) | High (Requires active agents) | Moderate (Lightweight agents) |
| Audit Trail | Generic cloud logs | Local AD logs | Detailed user-specific action logs |
| Access Control | Basic cloud permissions | On-premises AD policies | Fine-grained RBAC (Row/Field level) |
| AI/LLM Suitability | Low (Identity lost at data layer) | Low (Identity lost at data layer) | High (Preserves identity for AI queries) |
| Scalability | High (Cloud-native) | Moderate (Agent-dependent) | High (Kubernetes/Horizontal scaling) |
Ultimately, the right choice depends on your organization’s needs. If avoiding cloud credential storage is a priority, PTA might be the way to go. For those who value simplicity, PHS could be a better fit. But if your AI systems require user-specific entitlements and detailed compliance tracking, DreamFactory Identity Passthrough offers the most control - especially critical given that 79% of cyberattacks exploit legitimate credentials.
Conclusion
Selecting the right identity passthrough method for your hybrid AI deployment depends on two key factors: the level of control you require and what assets you need to safeguard. For those prioritizing simplicity and minimal on-premises infrastructure, Password Hash Synchronization (PHS) is a solid option, though account state changes can take up to two minutes to sync. On the other hand, Pass-Through Authentication (PTA) is ideal if your security policies prohibit storing any form of passwords in the cloud and you need instantaneous enforcement of on-premises account lockouts and sign-in restrictions.
That said, when AI systems interact with internal databases, neither PHS nor PTA fully addresses the challenge at the data layer. These methods focus on authentication during sign-in but don’t maintain user identity when AI agents execute database queries. This is where DreamFactory Identity Passthrough becomes essential - it carries the end-user's identity all the way to the database, enabling AI systems to respect row-level and field-level security. By doing so, it eliminates the risks associated with broad service accounts and reduces the potential damage from compromised sessions.
With 62% of organizations identifying regulatory compliance as a major driver for hybrid architectures, the need for robust solutions is clear. If your AI systems must operate within user-specific boundaries, DreamFactory offers unmatched control and detailed audit trails that traditional methods simply can’t provide. As DreamFactory aptly states:
"Every AI action is bounded by your policies and leaves a trail. Visibility without another shadow system".
FAQs
Why do hybrid AI systems lose user identity at the database layer?
Hybrid AI systems face a critical challenge at the database layer: they lose track of individual user identities. This happens because traditional database connections rely on service accounts with broad permissions. These accounts operate without associating actions to specific users, making it difficult to enforce access controls tailored to individuals or to trace user activities accurately.
When should I choose PHS vs. PTA in a hybrid AI setup?
If you're looking for a way to simplify password management and authentication by syncing password hashes to the cloud, go with PHS (Password Hash Synchronization). On the other hand, choose PTA (Pass-through Authentication) if you need secure, direct access to your on-premises domain controllers. PTA ensures encrypted network traffic and works smoothly with your current identity setup.
How does DreamFactory enforce row-level and field-level access for AI queries?
DreamFactory uses role-based access control (RBAC) and identity passthrough to enforce row-level and field-level access for AI queries. This setup ensures that each query is tied to the user's identity, applying rules that restrict access to specific rows or fields according to their permissions. These safeguards allow secure AI interactions with enterprise data while staying aligned with the existing authentication framework.
Related Blog Posts
Kevin Hood is an accomplished solutions engineer specializing in data analytics and AI, enterprise data governance, data integration, and API-led initiatives.
























 Blog
Blog
